Identity Security Solutions Across Critical Sectors
Deploy Dynamic Partial Identity to reduce identity exposure, prevent reuse, replay, and large-scale misuse, and strengthen trust across regulated ecosystems.
Designed for government ID programs, payment networks, and online identity platforms.
Government Identity Systems
Dynamic Partial Identity enables governments to replace static identifiers with renewable, partial identity values, significantly reducing the risk of misuse, replay, and large-scale compromise across identity ecosystems.
Ānśik ID™ for Government supports both software-based and hardware smart card deployments, allowing issuing authorities to select the appropriate Programmable Identifier Assurance Level (PIAL™) based on policy, risk posture, and regulatory requirements.
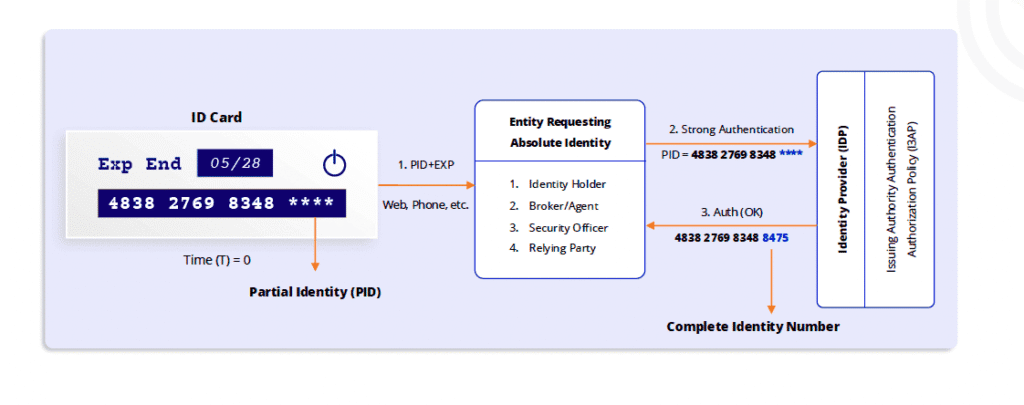
Government-issued credentials expose only a time-bound Partial Identity Value (PID), while the complete citizen identity is reconstructed securely by authorised systems under policy control.
Ānśik ID™ for Government supports both software-based and hardware smart card deployments, allowing issuing authorities to select the appropriate Programmable Identifier Assurance Level (PIAL™) based on policy, risk posture, and regulatory requirements.
Payment Industry
Dynamic Partial Identity protects sensitive payment identifiers such as the primary account number (PAN), expiry date, and security codes by replacing static values with renewable, partial identity representations. This significantly reduces exposure across both card-present and card-not-present environments.
Digital wallets and mobile payment applications remain linked to underlying card credentials and accounts. Ānśik ID™ extends protection to these wallet-linked identities, ensuring that compromise of a merchant, device, or wallet interface does not expose reusable payment credentials.
Ānśik ID™ for Payments supports both software-based and hardware smart card deployments, enabling payment networks and issuers to apply appropriate Programmable Identifier Assurance Levels (PIAL™) based on transaction risk and regulatory obligations.
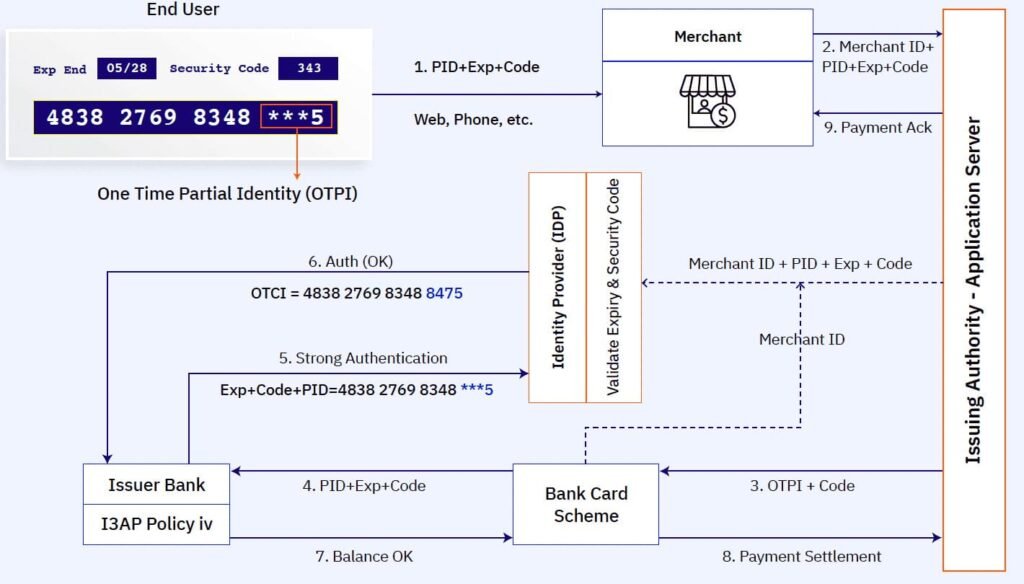
Each transaction uses a one-time partial identity, preventing reuse and replay across merchants and channels.
Online Identities Platforms
Dynamic Partial Identity replaces static identifiers with renewable, context-bound identity values that cannot be reused outside their intended session or service. Ānśik ID™ introduces One-Time Usernames (OTUN) and renewable authentication credentials, reducing the effectiveness of phishing, replay, and credential-stuffing attacks across digital platforms.
Because complete identities are never exposed to relying services, compromise of a website, application, or identity store does not yield reusable credentials. Identity fragments are time-limited, service-bound, and unusable outside their authorised conditions.
Ānśik ID™ for Online Identity supports both software-based and hardware-backed deployments, allowing organisations to apply the appropriate Programmable Identifier Assurance Level (PIAL™) based on service sensitivity and risk posture.
This approach strengthens existing authentication frameworks without requiring end-user retraining and remains compatible with modern federation, single sign-on (SSO), and identity-provider ecosystems.
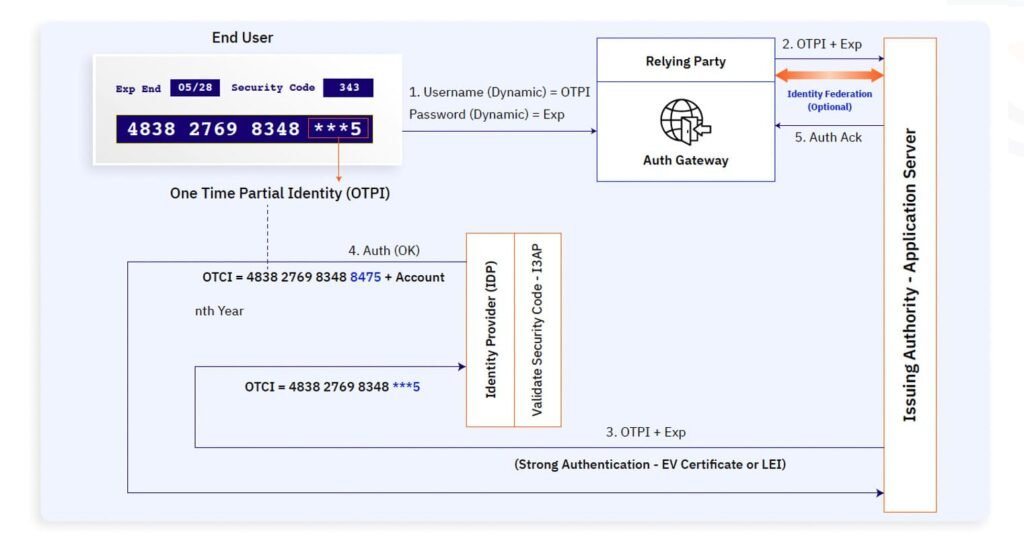
Dynamic usernames and time-bound credentials replace static login identifiers, reducing phishing and credential-reuse risks.
